An Ars story from earlier this month reported that iPhones expose the unique identifiers of recently accessed wireless routers, which generated no shortage of reader outrage. What possible justification does Apple have for building this leakage capability into its entire line of wireless products when smartphones, laptops, and tablets from competitors don’t? And how is it that Google, Wigle.net, and others get away with publishing the MAC addresses of millions of wireless access devices and their precise geographic location?
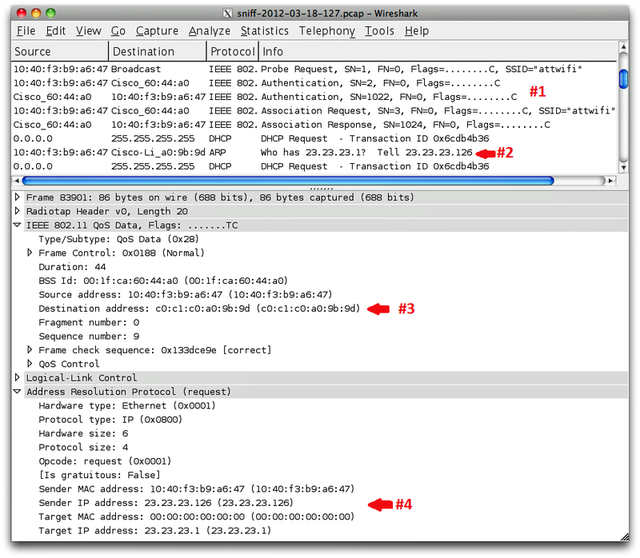
Some readers wanted more technical detail about the exposure, which applies to three access points the devices have most recently connected to. Some went as far as to challenge the validity of security researcher Mark Wuergler’s findings. “Until I see the code running or at least a youtube I don’t believe this guy has the goods,” one Ars commenter wrote.
According to penetration tester Robert Graham, the findings are legit.
Read the comments on this post
View the original here:
Anatomy of a leak: how iPhones spill the ID of networks they access