As a security professional who gets paid to hack into high-value networks, Mark Wuergler often gets a boost when his targets use smartphones, especially when the device happens to be an iPhone that regularly connects to Wi-Fi networks.
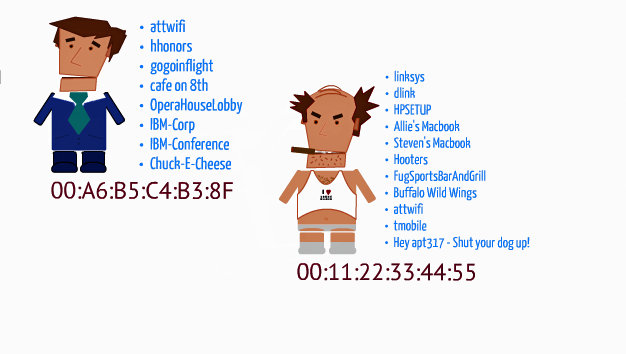
That’s because the iPhone is the only smartphone he knows of that transmits to anyone within range the unique identifiers of the past three wireless access points the user has logged into. He can then use off-the-shelf hardware to passively retrieve the routers’ MAC (media access control) addresses and look them up in databases such as Google Location Services and the Wireless Geographic Logging Engine. By allowing him to pinpoint the precise location of the wireless network, iPhones give him a quick leg-up when performing reconnaissance on prospective marks.
Read the comments on this post
Taken from:
Loose-lipped iPhones top the list of smartphones exploited by hacker