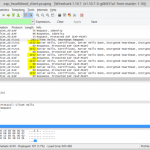
 A packet capture showing Cupid attacking a wireless network. SysValue It just got easier to exploit the catastrophic Heartbleed vulnerability against wireless networks and the devices that connect to them thanks to the release last week of open source code that streamlines the process of plucking passwords, e-mail addresses, and other sensitive information from vulnerable routers and connected clients. Dubbed Cupid, the code comes in the form of two software extensions. The first gives wireless networks the ability to deploy “evil networks” that surreptitiously send malicious packets to connected devices. Client devices relying on vulnerable versions of the OpenSSL cryptography library can then be forced to transmit contents stored in memory. The second extension runs on client devices. When connecting to certain types of wireless networks popular in corporations and other large organizations, the devices send attack packets that similarly pilfer data from vulnerable routers. The release of Cupid comes eight weeks after the disclosure of Heartbleed , one of the most serious vulnerabilities to ever hit the Internet. The flaw, which existed for more than two years in OpenSSL, resides in “heartbeat” functions designed to keep a transport layer security (TLS) connection alive over an extended period of time. Read 5 remaining paragraphs | Comments
A packet capture showing Cupid attacking a wireless network. SysValue It just got easier to exploit the catastrophic Heartbleed vulnerability against wireless networks and the devices that connect to them thanks to the release last week of open source code that streamlines the process of plucking passwords, e-mail addresses, and other sensitive information from vulnerable routers and connected clients. Dubbed Cupid, the code comes in the form of two software extensions. The first gives wireless networks the ability to deploy “evil networks” that surreptitiously send malicious packets to connected devices. Client devices relying on vulnerable versions of the OpenSSL cryptography library can then be forced to transmit contents stored in memory. The second extension runs on client devices. When connecting to certain types of wireless networks popular in corporations and other large organizations, the devices send attack packets that similarly pilfer data from vulnerable routers. The release of Cupid comes eight weeks after the disclosure of Heartbleed , one of the most serious vulnerabilities to ever hit the Internet. The flaw, which existed for more than two years in OpenSSL, resides in “heartbeat” functions designed to keep a transport layer security (TLS) connection alive over an extended period of time. Read 5 remaining paragraphs | Comments
See more here:
Meet “Cupid,” the Heartbleed attack that spawns “evil” Wi-Fi networks





