Is turnabout fair play? A handful of Anons have found themselves on the wrong end of a hack in the wake of the US government takedown of Megaupload. On January 20, just one day after Megaupload founder Kim Dotcom was arrested in New Zealand, an unknown attacker slipped code from the infamous Zeus Trojan into the slowloris tool used by members of Anonymous to carry out DDoS attacks on websites that have drawn their ire. As a result, many of those who participated in DDoS attacks targeted at the US Department of Justice, music label UMG, and whitehouse.gov also had their own PCs compromised.
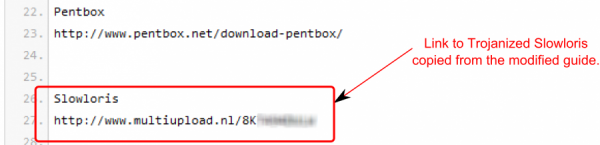
Security firm Symantec details how some Anons ended up with Zeus on their systems. After modifying the Slowloris source to include code for the Zeus trojan on January 20, the attacker changed a couple of Pastebin guides used to bring would-be DDoSers up to speed to show a new URL for downloading the Slowloris tool.
Each time Slowloris was downloaded and launched after the 20th of January, a Zeus botnet client was installed too. The Zeus client then stealthily downloaded a “clean” version of Slowloris to replace the modified copy in an attempt to conceal its existence on the infected PC. In the meantime, the Zeus trojan did its usual dirty work: capturing passwords and cookies, as well as banking and webmail credentials, and sending them off to a command-and-control server.
Symantec’s research shows the modified version of Slowloris was widely downloaded. “This Anonymous DoS tool on PasteBin has become quite popular among the Anonymous movement with more than 26,000 views and 400 tweets referring to the post,” noted Symantec’s official blog.
The compromised version of Slowloris is no longer linked to on Pastebin: it appears that coverage of the shenanigans pulled on Anonymous has resulted in what looks to be a link to the correct verison of Slowloris being restored to the Pastebin guide.
Having Zeus installed on one’s PC is absolutely no fun at all, so those who have downloaded the compromised version of Slowloris are going to have their hands full trying to hunt down and eradicate the trojan. Indeed, we see a number of clean OS installs in the immediate future for those who participated in DDoS attacks after the Megaupload takedown.
Read the comments on this post
Visit link:
Slowloris DDoS tool used by Anonymous hacked to include Zeus trojan