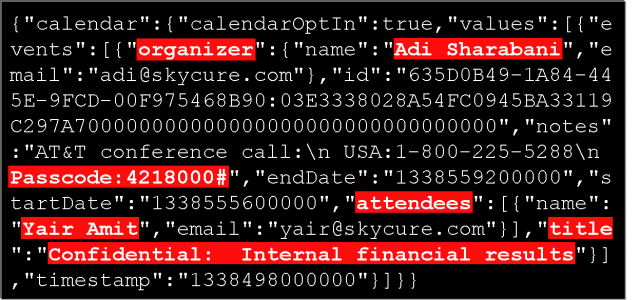
Today’s not a good day to be a LinkedIn user—doubly so if you use LinkedIn’s iPhone or Android app. Researchers have discovered that the app scrapes users’ Calendar items and sends the data back up to its servers, even when those Calendar items were created outside of the LinkedIn app. The scraped data includes participant lists, subject of the entry, time of the meeting, and any attached meeting notes (such as dial-in details and passcodes).
The LinkedIn app manages to gain access to your Calendar items because it has a feature that allows you to view your calendar from within the app itself. According to security researchers Yair Amit and Adi Sharabani, the app then transmits this information to LinkedIn’s servers without any clear indication to the user that this is hapening—a throwback to the Path controversy that revealed the social networking app (among many others) had been transmitting users’ contact lists to a remote server without explicit user consent.
Amit and Sharabani plan to present their report at a cyber security conference in Tel Aviv on Wednesday. In their report seen by Ars, they note that the information being collected by the LinkedIn app has no apparent relevance to the app’s functionality, though they don’t believe LinkedIn has included this functionality maliciously. “However, we are concerned by the fact it collects and sends-out sensitive information about its users, without a clear indication and consent,” the researchers wrote.
More here:
Your iPhone calendar isn’t private—at least if you use the LinkedIn app




